Leveraging Liveness Detection to Protect Against Face Recognition Attacks
Last time (part 1)we talked about various ways to hack a face recognition system. Similarly to the various attacking methods, there are also many ways to prevent your face from being accessed by others. All of them are well-developed and could serve as your best partner for a convenient and futuristic lifestyle.
Single Frame Liveness
This is the basic form of liveness detection where one RGB image is used for detection. The inference time can be as short as under 100ms, and the only device required is a decent camera. However, this method is also the most vulnerable since the least amount of information is used.
Multiple Frame Liveness
Multiple frame liveness increases the accuracy of liveness detection by looking at not one, but multiple images of the same face over a period of time. This method preserves the advantage that no other camera is used, making it cheap hardware-wise, but at the cost of more time spent on each detection. The accuracy can be further boosted by the use of optical flows, reflections (see next section), and other techniques.
Reflection Liveness
Vendors like iProov provide liveness detection through colored light reflection, which involves an app displaying a randomly generated sequence of strong colored light. This is especially useful for deep fake attacks and is currently one of the most robust detection algorithms out there. Other variants include using random appearing frequencies instead of colors, or the difference between the light/dark frames to perform the detection.
Binocular Liveness
How about the other way around? Binocular liveness utilizes additional camera devices like infrared cameras to greatly increase the accuracy while maintaining the fast speed. They're robust but come with the baggage of being device-dependent and potentially pricier. (Fig. 1)

Interactive Liveness
Interactive liveness is a cooperative method that asks users to perform actions like turning their heads, blinking, or smiling. However, based on reports, almost a quarter of users abandon the face recognition process when asked to perform tasks.
Standards and Certification
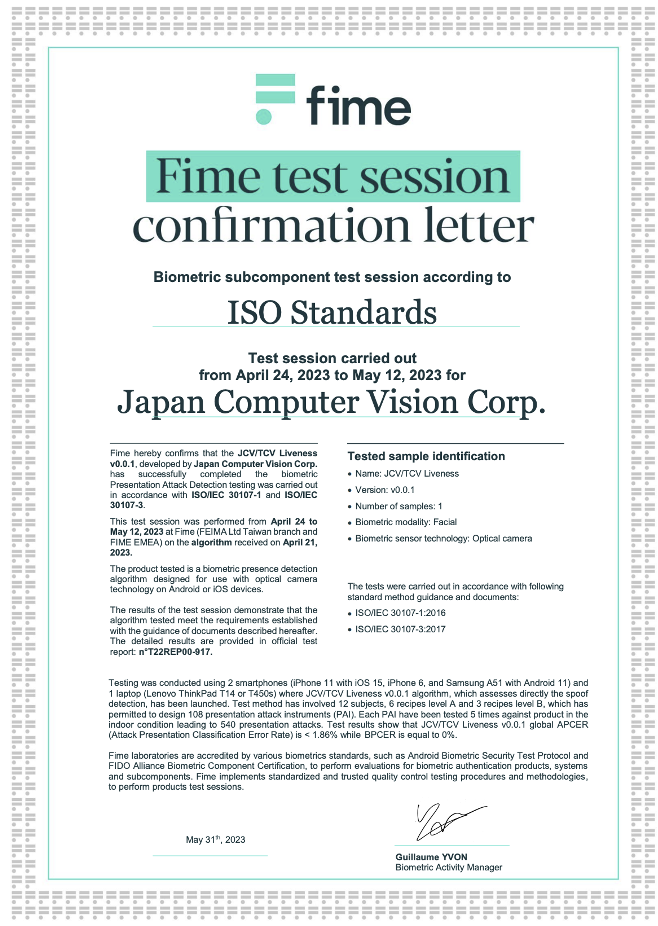
For smaller biometric-providing companies, it is no easy deal to prepare all the testing environments needed for an ISO certificate. In this case, you may have to rely on professional third-party testing organizations. There are typically two ways to prove you have a reliable product. You can:
Look out for a reliable testing vendor. Ensure that their solutions are ISO 30107 or FIDO certified. Vendors like Fime or iBeta are the most common picks. Here is a list of FIDO-certified vendors for your reference.
List of FIDO-certified vendors
A Fime certificate will look like this:
Another method you can use to prove the effectiveness of your technology is to compete in online liveness contests. Organizations like NIST hold these kinds of contests annually and have become the battlegrounds where companies fight for the crown of the best solution.

Try in on Your Own
Theory and data are one side of the coin. Feeling the solution in action completes the circle. Visualization tools like the JCV Model Explorer bridge the gap between numbers and real-world performance. For those keen to delve deeper, tutorials await!
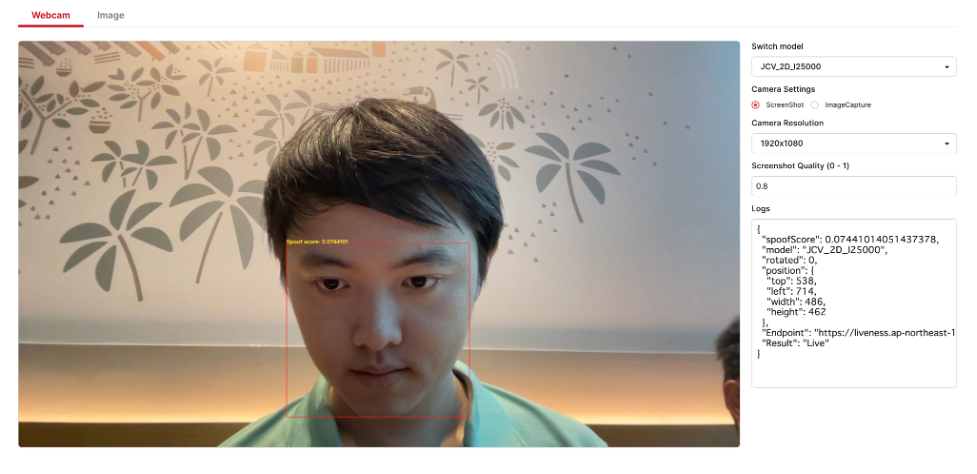
Embark on this face-forward journey, ensuring that as technology evolves, so do our defenses against potential threats. Dive in, explore, and fortify.


